As the Internet of Things (IoT) continues to revolutionize industries worldwide, the integration of secure communication protocols like SSH becomes increasingly critical. IoT SSH applications examples demonstrate the power of combining IoT devices with secure shell (SSH) technology to enhance security, remote management, and automation. In this article, we will delve into the world of IoT SSH applications, examining their use cases, benefits, and implementation strategies.
The growing number of interconnected devices in smart homes, industrial environments, and healthcare systems highlights the need for robust security measures. IoT SSH applications provide a secure channel for communication, ensuring that sensitive data remains protected from unauthorized access. This article aims to provide an in-depth understanding of IoT SSH applications, making it an essential read for developers, engineers, and decision-makers in the IoT ecosystem.
With the increasing demand for secure and efficient IoT solutions, understanding the role of SSH in IoT applications is crucial. By exploring real-world examples and case studies, we will uncover the potential of IoT SSH applications and how they can be leveraged to drive innovation and efficiency in various sectors.
Read also:Gypsy Rose Boyfriend Age Unveiling The Truth Behind The Relationship
Table of Contents
- Introduction to IoT SSH
- Benefits of IoT SSH Applications
- Common IoT SSH Use Cases
- Key Features of IoT SSH Applications
- Security Aspects of IoT SSH
- Tools for IoT SSH Implementation
- Examples of IoT SSH Applications
- Best Practices for IoT SSH Deployment
- Challenges in IoT SSH Integration
- Future of IoT SSH Applications
Introduction to IoT SSH
The Internet of Things (IoT) involves a network of interconnected devices that communicate and exchange data. As IoT expands, so does the need for secure communication protocols. Secure Shell (SSH) plays a pivotal role in ensuring secure data transfer between IoT devices. SSH provides encrypted communication, authentication, and secure file transfer, making it an ideal choice for IoT applications.
How SSH Works in IoT
SSH establishes a secure connection between devices by encrypting all data transmissions. This ensures that even if data is intercepted, it remains unreadable without the correct decryption keys. In IoT, SSH can be used for remote management, secure updates, and data synchronization, enhancing the overall security and reliability of IoT systems.
Benefits of IoT SSH Applications
Implementing SSH in IoT applications offers several advantages, including enhanced security, simplified remote management, and improved operational efficiency.
Enhanced Security
SSH encrypts all data transmissions, protecting sensitive information from unauthorized access. This is particularly important in IoT systems, where devices often handle personal or confidential data.
Simplified Remote Management
With SSH, administrators can remotely manage IoT devices securely. This eliminates the need for physical access, saving time and resources while maintaining system integrity.
Improved Operational Efficiency
SSH streamlines processes such as firmware updates, configuration changes, and data backups, ensuring that IoT systems operate efficiently and reliably.
Read also:Otto Kilcher Death A Comprehensive Look Into The Life And Tragic End Of An Iconic Figure
Common IoT SSH Use Cases
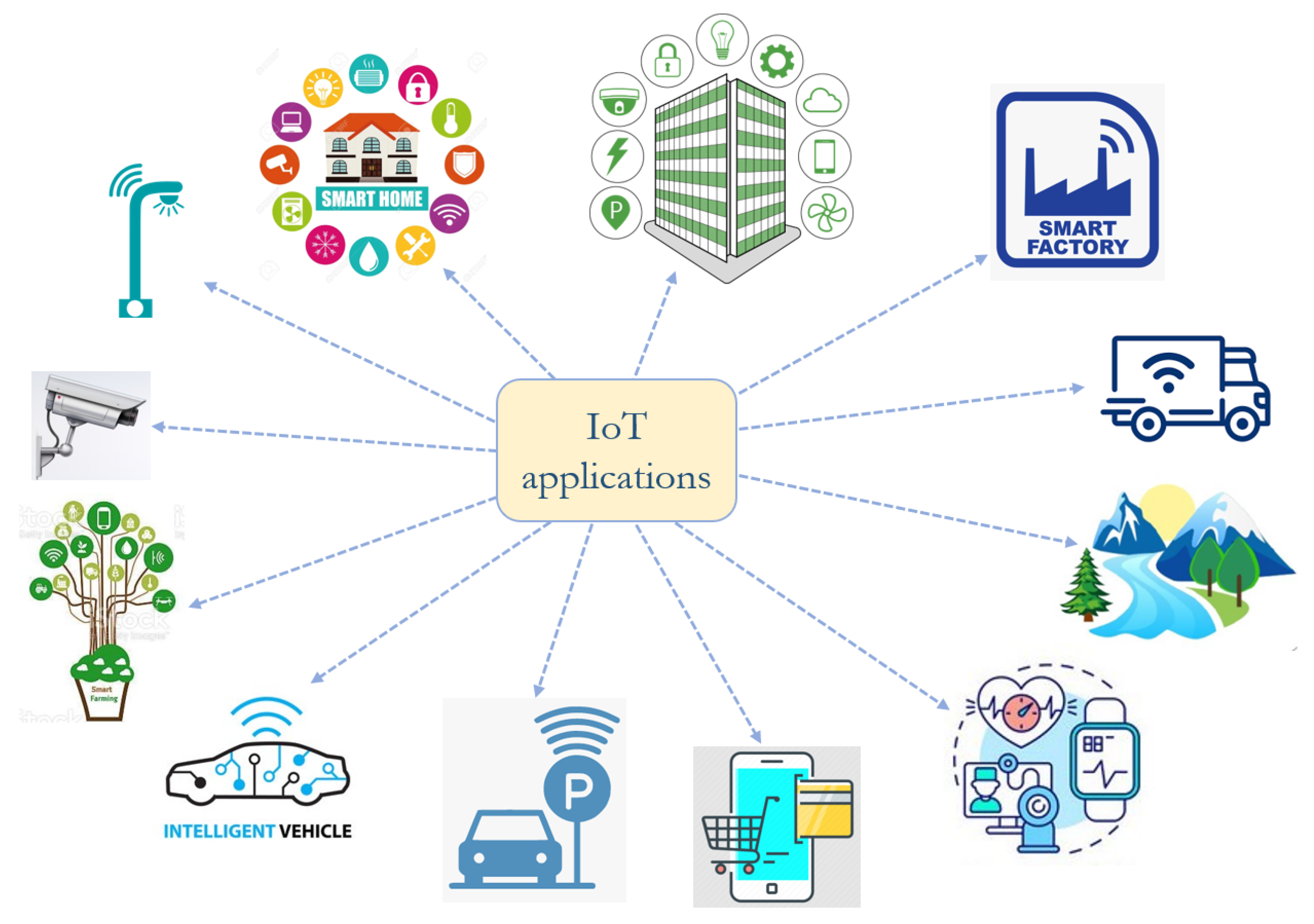
IoT SSH applications are versatile and can be applied across various industries. Below are some common use cases:
- Smart Homes: SSH enables secure communication between smart home devices, ensuring that commands and data are transmitted safely.
- Industrial IoT (IIoT): SSH is used for secure remote monitoring and control of industrial equipment, reducing downtime and improving productivity.
- Healthcare IoT: In healthcare, SSH secures the transmission of patient data between medical devices and servers, maintaining compliance with data protection regulations.
Key Features of IoT SSH Applications
Effective IoT SSH applications possess several key features that contribute to their success:
Encryption
All data transmitted through SSH is encrypted, ensuring confidentiality and integrity.
Authentication
SSH uses strong authentication methods, such as public-key cryptography, to verify the identity of devices and users.
Remote Access
SSH allows secure remote access to IoT devices, enabling administrators to manage systems from anywhere.
Security Aspects of IoT SSH
Security is a top priority in IoT SSH applications. Below are some critical security aspects to consider:
Data Privacy
SSH ensures that all data transmissions remain private and protected from unauthorized access.
Access Control
Implementing strict access control policies helps prevent unauthorized access to IoT devices and networks.
Regular Updates
Regularly updating SSH software and firmware ensures that vulnerabilities are patched, maintaining system security.
Tools for IoT SSH Implementation
Several tools and platforms facilitate the implementation of IoT SSH applications:
- OpenSSH: A widely used open-source SSH implementation for securing communications between IoT devices.
- Dropbear: A lightweight SSH server and client suitable for resource-constrained IoT devices.
- Paramiko: A Python library for implementing SSH functionality in IoT applications.
Examples of IoT SSH Applications
Real-world examples of IoT SSH applications demonstrate their versatility and effectiveness:
Smart Agriculture
SSH enables secure communication between sensors and control systems in smart agriculture, optimizing resource usage and improving crop yields.
Smart Grids
In smart grids, SSH secures the transmission of energy consumption data, ensuring accurate billing and efficient energy management.
Smart Cities
SSH enhances the security of smart city infrastructure, protecting data from traffic management systems, environmental sensors, and public safety networks.
Best Practices for IoT SSH Deployment
To ensure successful deployment of IoT SSH applications, consider the following best practices:
- Use strong passwords and public-key authentication to enhance security.
- Regularly update SSH software to address security vulnerabilities.
- Implement network segmentation to isolate IoT devices from other systems.
Challenges in IoT SSH Integration
Integrating SSH into IoT systems presents several challenges:
Resource Constraints
Resource-constrained IoT devices may struggle to handle the computational demands of SSH encryption.
Complexity
Implementing SSH in large-scale IoT systems can be complex, requiring careful planning and management.
Interoperability
Ensuring interoperability between different IoT devices and platforms can be challenging, especially when using SSH.
Future of IoT SSH Applications
The future of IoT SSH applications looks promising, with advancements in technology driving innovation:
Quantum-Safe Cryptography
As quantum computing becomes more prevalent, quantum-safe cryptography will play a crucial role in securing IoT SSH applications.
Edge Computing
Edge computing will enhance the performance and security of IoT SSH applications by processing data closer to the source.
AI Integration
Integrating AI with IoT SSH applications will enable smarter decision-making and automation, further improving system efficiency.
Conclusion
In conclusion, IoT SSH applications examples showcase the potential of combining IoT with secure communication protocols like SSH. By enhancing security, simplifying remote management, and improving operational efficiency, IoT SSH applications are transforming industries worldwide. To fully leverage their capabilities, it is essential to follow best practices and address the challenges associated with their deployment.
We invite you to share your thoughts and experiences with IoT SSH applications in the comments section below. Additionally, explore our other articles to deepen your understanding of IoT and related technologies. Together, let's shape the future of secure and intelligent IoT systems!